As you probably know the ability to Remote Control a user in RDS (shadowing) was removed from Windows Server 2012. I briefly talked about that in a Customer Review I wrote for blogs.msdn.com. In the R2 upgrade of Windows Server 2012, Remote Control has been reintroduced! I briefly discussed this in the blog post What's New in Windows Server 2012 R2 Virtual Desktop Infrastructure and Remote Desktop Services (more details!)
Now that the preview bits for Windows Server 2012 R2 have been released during Tech Ed Europe in Madrid, I’m able to show Remote Control (shadowing) in Windows Server 2012 R2 in greater detail.
With Windows Server 2012, there are 2 options to perform the Remote Control of a user session. Using the Server Manager GUI or using a the Command Line.
Remote Control using Server Manager GUI
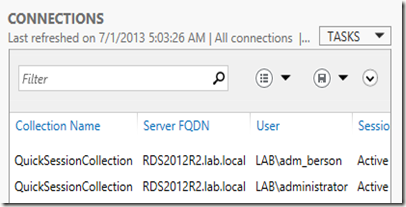
Open the Server Manager Console and select Remote Desktop Services. You now have two options to find the user you want to Remote Control. Click on “Collections” and the look at the Connections section. This view contains all active or idle sessions within every Session Collection as part of the deployment.
Or, if you know the Session Collection under which the user is active, in stead of clicking on “Collections”, click on the collection in question and then look at the Connections section.
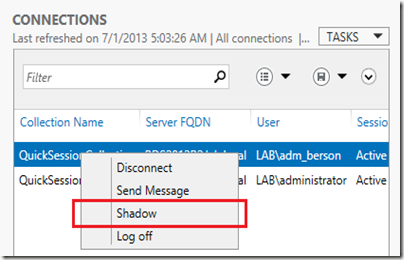
To Remote Control a user, right click the user and choose Shadow
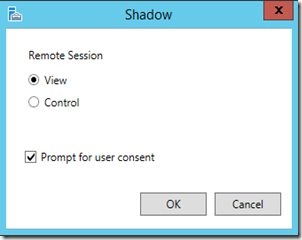
You will then be prompted asking if you would like to view or control the session and if the users needs to be prompted, which can also be enforced using GPO.
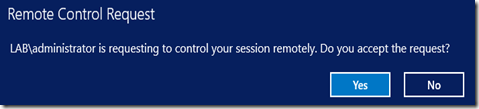
The user in question will receive an authorization request as shown below.
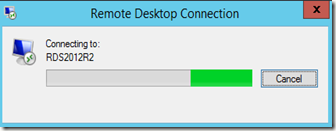
While waiting for the users response the administrator is represented with the dialog below.
If the user clicks No or does not respond within 30 seconds the administrator that launched the Remote Control will be presented with a “The operator or administrator has refused the request”.
The 30 seconds is also configurable suing the GPO:
Computer Configuration\Policies\Administrative Templates\Windows Components\Remote Desktop Services\Remote Desktop Session Host\Connections\Set Rules for Remote Control of Remote Desktop user Session
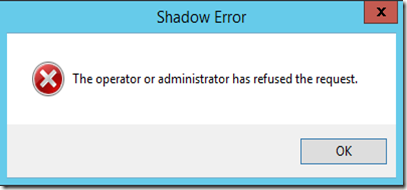
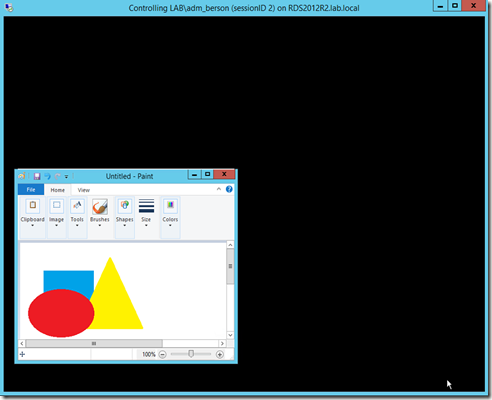
If he chooses to accept, the Remote Control will start and the administrator will be presented with the remotely controlled session easily recognizable by looking at the name of the window as shown below.
Remote Control using the Command line
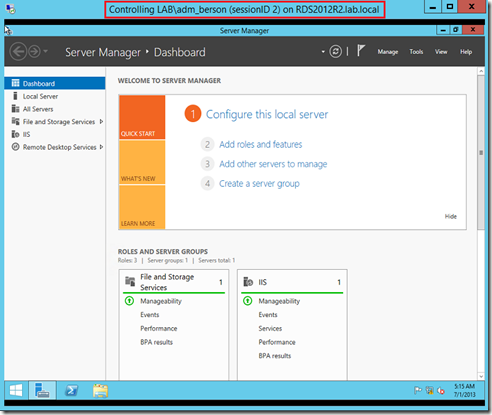
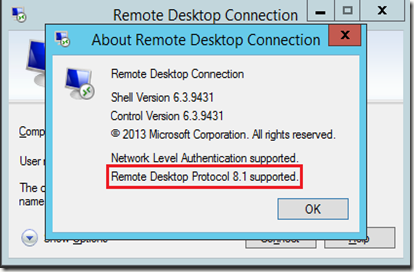
The second method to Remote Control is by using the command line. In order to be able to perform the command line Shadow the client machine must be running at least Remote Desktop Client 8.1 (which at this point is only available for Windows 8.1 (preview) or Windows Server 2012 R2 (preview), but will be become available for Windows 8 and Windows Server 2012 in the future.
The reason for this requirement is that the shadowing option has become part of the mstsc.exe executable itself.
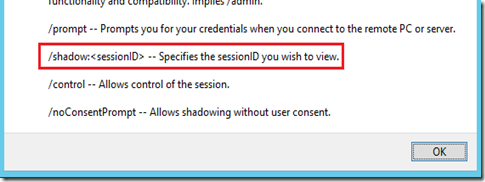
To be more precise, the shadowing is now a command line parameter of mstsc.exe which can be confirmed by running mstsc.exe /help, which will result in the screenshot below.
The syntax to shadow a session is as follows:
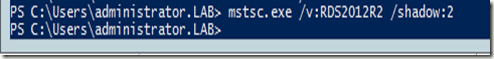
mstsc /v:<ServerName> /shadow:<SessionID>
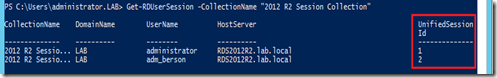
We obviously first need to find out the ID of the session we want to Remote Control. The Session ID can be found by running the PowerShell command “”Get-RDUserSession” (make sure you first import the module RemoteDesktop) and is retrieved in the UnifiedSessionId column.
And while inside the PowerShell console it’s probably most convenient to do the mstsc command from within there is as well.
The authorization process is the same compared to launching the Shadow option from the GUI, however, by default the command line will start the Remote Control in “View” mode. If you want to be able to interact with the session the parameter /control also needs to be specified. If you want to bypass the authorization prompt, use the /noConsentPrompt option.
In the introduction I also mentioned that shadowing has not only been reintroduced in R2 but also improved. We’re now also able to Shadow a Remote App, which was previously not supported. And also it now supported to shadow a client session running multiple monitors.
Shadowing a Remote App
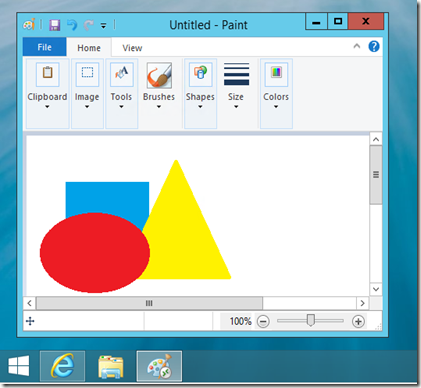
As an example we launch Paint as a Remote App
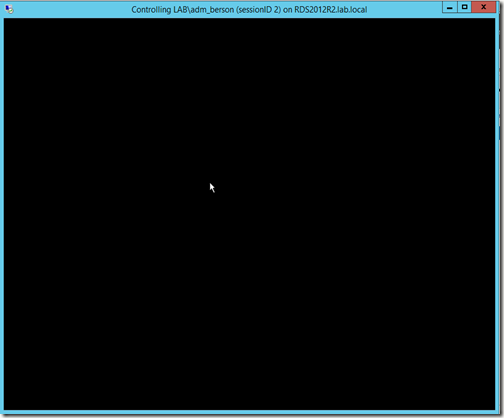
If you perform a Remote Control on this user Session (and after running through the same authorization process) you are represented with the screen below. Because the user we’re shadowing does not have a desktop we see a black screen presenting the users desktop.
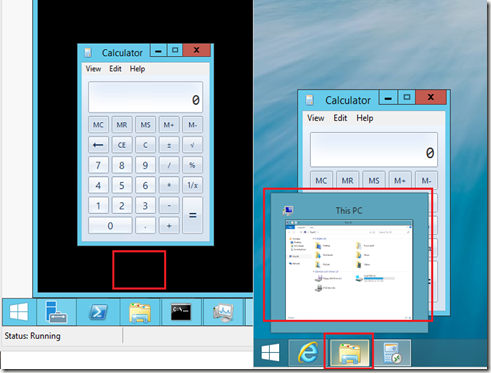
As you might know, if a user runs more than 1 Remote Apps, additionally launched Remote Apps all run in the same user session (and thus same Session ID). Therefor, if a user would run multiple Remote Apps, they will all be visible for the administrator who is shadowing, as shown below.

Do note that if the end user minimizes the Remote App, it will become invisible for the administrator doing to Remote Control. So if all Remote Apps are minimized the administrator will end of with a black screen.
Also, note that since the black screen represents the user local desktop, I the administrator chose the Control option and would move to the lower left part of the black screen that triggers the local start menu. In the screenshot below the administrator moved the cursor to the area marked by the red square on the left. That causes the File Explorer on the local user’s client (on the right) to show a preview pane.
The administrator obviously cannot interact with the local desktop by performing left or right clicks, but the experience above is something to be aware of.
The black screen does not occur when shadowing a full desktop that the end user minimizes. The admin will still be able to interact with a minimized full desktop session.
Permissions
In order to be able to perform Shadowing you need permissions. If no permissions are in place it will result in the error below.
Being local administrator on the destination server obviously works. However, to allow non-administrators permissions to shadow you can use the following command which is also applicable for Windows Server 2008 R2 (Credits for this command go to fellow RDS MVP TP who posted this on TechNet Forum.
wmic /namespace:\\root\CIMV2\TerminalServices PATH Win32_TSPermissionsSetting WHERE (TerminalName="RDP-Tcp") CALL AddAccount "domain\group",2
Than concludes this blog post on the reintroduction or Remote Control (shadowing) in Windows Server 2012 R2.
Happy shadowing !!


Hi, Freek!
ReplyDeleteThank you, very useful article, if you're interested, I posted article how to configure Remote Assistance in place of the Remote Control (shadowing) on terminal server 2012, as workaround, Russian Wiki - http://social.technet.microsoft.com/wiki/ru-ru/contents/articles/20041.remote-assistance-windows-server-2012.aspx
Finally - that is awesome news.
ReplyDeletehi. how can I remote control sessions if I can't see collections with user sessions. I installed remote desktop role and when I choose it in server manager it says that I've entered as local administrator and if I want to remote control I need to enter as domain user. what does it mean? should I install DNS and Active Directory to remote control sessions?
ReplyDeleteDid you ever get an answer to this? I'm having the same problem
DeleteJust tried to do this on a Windows 2012 R2 Server and its giving me access denied, Domain Administrator is in the Windows 7 Client SP1, The RDS on the client is v8.1 as soon as I click shadow no matter whether I chose View or control it comes back immediately with Access Denied, the GPO for Enable Remotedesktop is enabled, i.e. the one that allows shadowing without user control. What I have noticed is if I do the Get-RDUserSession it shows say sessionID 6, if I then do mstsc /v: /shadow:6 its giving the error the session id does not specify a valid session, even though the ID is that given when i do the get-rdusersession anyone got any idea on this ?
ReplyDeleteKevin... Did you ever find an answer to this? I have the exact same issue as you described. Access denied as well as the session ID problem. I cannot remote assist any VD.
ReplyDeleteTHX a lot :)
ReplyDeletePorque Microsoft retiro capacidad de controlar a distancia un usuario en RDS (sombreado) fue retirado de Windows Server 2012, si las versiones anteriores contaban con esta caracteristica que ayudaba al administrador del servidor
ReplyDeleteJJuarez,
ReplyDeletePlease keep comments in English
Hi. When I try and run the wmic command I get "invalid method parameters"
ReplyDeleteIs there any part of the command where you need to enter your own details?
I have modified the domain\group settings but still get the same error.
Shadowing works very well, however if the end user has more than 1 monitor the session I see shows both monitors on a single screen which makes it very difficult to see what I am doing in their session. Is there any way to work around this limitation to either increase the size of their screen or only see one of the end user's monitor?
ReplyDeleteI have the same issue as Bill. Have looked around but havent found any solution for this yet. any ideas?
ReplyDeleteIs there a workaround to allow Remote Control when the server is not in a domain? I don't have 'Connections' when I go into Server Manager > Remote Desktop Services. All I have are Overview and Servers
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteI am also facing issues for supporting shadowing of multiple monitors. The screensize is extremely small and both the monitors fit in a single screen which makes it extremely difficult for work on shadowed session. Has anyone got a solution for this? Please if you can advice.
ReplyDeleteMe too, anyone know how to fix this? seems that "Smart Sizing" is enabled by default for shadowed sessions........
DeleteI have the same problem Adrii does. "How can I remote control sessions if I can't see collections with user sessions?"
ReplyDeleteHi Freek, in winserver 2012 is possible to have shadow?
ReplyDelete